A group of hackers has hijacked tens of thousands of Google’s Chromecast streaming dongles, Google Home smart speakers and smart TVs with built-in Chromecast technology in recent weeks by exploiting a bug that’s allegedly been ignored by Google for almost five years.
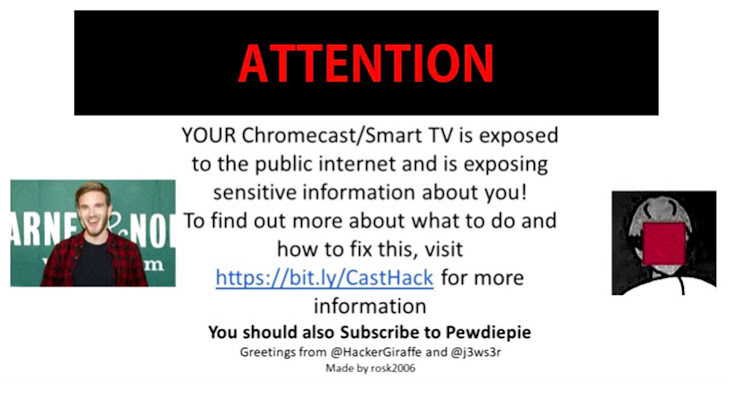
The attackers, who go by Twitter handles @HackerGiraffe and @j3ws3r, managed to hijack Chromecasts’ feeds and display a pop-up, spreading a security warning as well as controversial YouTube star PewDiePie propaganda.
The hackers are the same ones who hijacked more than 50,000 internet-connected printers worldwide late last year by exploiting vulnerable printers to print out flyers asking everyone to subscribe to PewDiePie YouTube channel.
This time, the hackers remotely scanned the internet for compatible devices, including Chromecasts, exposed to the internet through poorly configured routers that have Universal Plug and Play [UPnP] enabled by default.
The hackers then exploited a design flaw in Chromecast that allowed them to access the devices and hijack their media streams to display a video message (as shown below) on connected televisions without authentication.
“YOUR Chromecast/Smart TV is exposed to the public internet and is exposing sensitive information about you! To find more about what to do and how to fix this, visit https://bit.ly/CastHack for more information,” the message reads.
Besides security warnings, the hackers again took a chance to promote PewDiePie—a famous YouTuber from Sweden who is known for his game commentary and pranks and has had the most subscribers on YouTube since 2013.
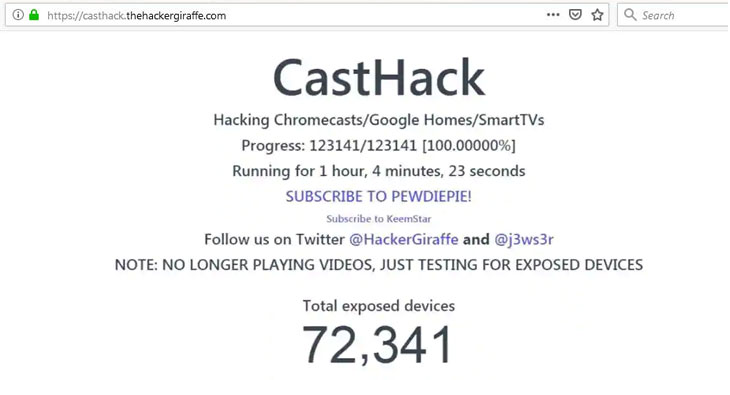
The hackers even set up a dedicated website (now been taken down) for their hack, which they dubbed “CastHack,” with a live counter displaying the total number of exposed devices and how many of them have been forced to play video in support of PewDiePie.
CastHack can be used to collect all kinds of data from victim’s homes, including which devices their Chromecasts or Google Home is connected to over Wi-Fi, which Bluetooth devices it was paired with, how long it has been on, which WiFi networks it had previously connected to and what alarms have been set.
Moreover, an attacker can also remotely force affected devices into playing media of their choice, rename devices, force factory reset or reboot the device, force it to forget all WiFi networks, or force the affected device to pair with new networks.
Interestingly, Google was made aware of the Chromecast bug multiple times since 2014 shortly after the streaming device was launched and also acknowledged the hack, but the company has decided to ignore the issue.
Several users have confirmed that their devices were compromised. Users can fix this issue by just changing their router settings, stop forwarding ports 8008, 8443 or 8009, as well as turning off its Universal Plug and Play (UPnP) feature until and unless it is needed.
UPnP comes enabled by default on every internet-connected device, creating a hole in your router’s security that could allow malware to infiltrate any part of your local network. Hackers have compromised UPnP several times in the past.